CoreLogic’s Digital Mortgage Platform (DMP) allows you to curate a frictionless mortgage process from application to closing. Using unmatched property-data insights and optimized workflows, this platform allows you to accelerate borrower verifications in the origination process creating a smoother digital lending experience for your clients.
Prioritize the consumer experience to build lasting partnerships. With online document signing and accurate hybrid closing solutions, you can expedite the digital mortgage process while building trust with clients.
Digital Mortgage Platform automates repetitive tasks to significantly lower human error risk while enhancing connections that accelerate overall lending processes and reduce operational costs.
Tailor digital mortgage workflows to suit lenders’ needs. CoreLogic’s DMP is customizable at scale, allowing for seamless first-party integrations and simplified loan lifecycles that dynamically deliver industry-leading experiences.
Modernize mortgage lending by empowering your loan officers to provide the exceptional client experiences that foster long-term business growth. With seamless integrations, efficient workflows, and a borrower-centric approach, your loan officers will be equipped to set your business up for success in the ever-changing mortgage industry.
With both mobile and desktop application interfaces, borrowers can easily apply for a mortgage wherever they are. This user-friendly interface is customizable, allowing lenders to include only the necessary questions for verification and offer auto-fill form option. Plus, lenders can customize the branding to create a cohesive ecosystem from the beginning of the mortgage process.
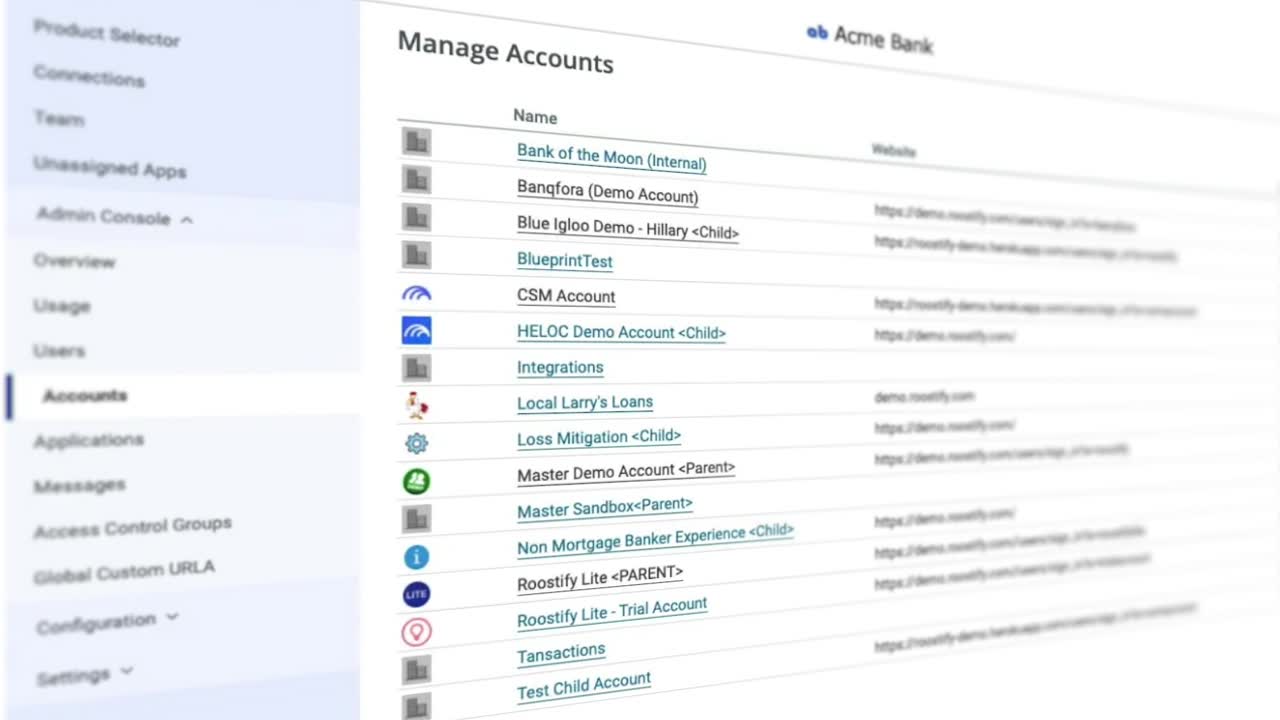
Upgrade your mortgage workflow management by tailoring the Digital Mortgage Platform interface to suit your needs. The running management list allows you to navigate between loans with just a few clicks. Monitor loan statuses in real-time and take care of outstanding tasks. Collaborate with the parties interacting with a loan, and ensure that loans are assigned to the appropriate parties for next steps.
The Digital Mortgage Platform helps facilitate smooth first-party integrations and partnerships that lower the cost of lending at scale. Integrations help you configure the platform to reduce friction in obtaining required clients materials and automating the repetitive operations within the loan lifecycle.
By combining CoreLogic’s AutomatIQ™ Borrower Income Analysis and SmartFees, the Digital Mortgage Platform automatically extracts income data for precise mortgage application analysis while also ensuring regulatory compliance, automate fee calculations, and a tiered view of loan scenarios.
Bridge the gap between borrower needs and lender operations with bi-directional transfers of data and documents through this LOS integration. Whether you have requests for additional information or you need to see a historical record of document submissions, ensure a smooth flow of information and assets between the point-of-sale (POS) platform and the loan origination system (LOS).


Digital Mortgage Platform offers a variety of support options for users. Review how-to guides or reach out to your representative for help at the following URL: https://mortgageplatform.corelogic.com/
CoreLogic’s Digital Mortgage Platform is an end-to-end mortgage origination solution that enables lenders to streamline operations, improve efficiencies, and enhance borrower experiences. The platform leverages advanced technology and data analytics to facilitate a seamless mortgage origination process.
The Digital Mortgage Platform give lenders a competitive edge in the dynamic mortgage industry. The platform offers a range of benefits, including improved efficiency, faster loan processing times, enhanced underwriting accuracy, reduced costs, optimized compliance, and a better borrower experience.
| The Digital Mortgage Platform includes advanced features, such as automated underwriting, comprehensive loan origination, document management, e-signatures, mobile access, data integration, etc. |
Yes, the Digital Mortgage Platform is designed to be flexible and customizable, catering to the specific requirements of each lending business. You can tailor features and tools to best suit your needs and meet your unique business goals.
Yes, the Digital Mortgage Platform is highly flexible. It offers a broad range of integration capabilities for seamless integration into other business systems and workflows. This capability enables easy data exchange, resulting in faster processing times.
Yes, the Digital Mortgage Platform provides an intuitive interface for borrowers to securely submit their documents online. The platform also supports automated document verification and validation.
Fill in the form below to contact us.
AutomatIQ Borrower Income Analysis does for income calculation what Digital Mortgage Platform does for point of sale. It is a single, intelligent workflow solution that helps you efficiently analyze and confidently calculate a borrower’s income in a fraction of the time.
Like our Digital Mortgage Platform, VOA helps you say goodbye to time-consuming and frustrating manual processes. VOA provides an easier and more secure way to collect asset information by going directly to your borrower’s financial institutions.
Verify every borrower, every time. Our streamlined VOE/I three-step waterfall workflow is designed to gather employment and income data for all borrowers via an instant verification step, an automated verification step, and if necessary, a manual verification.